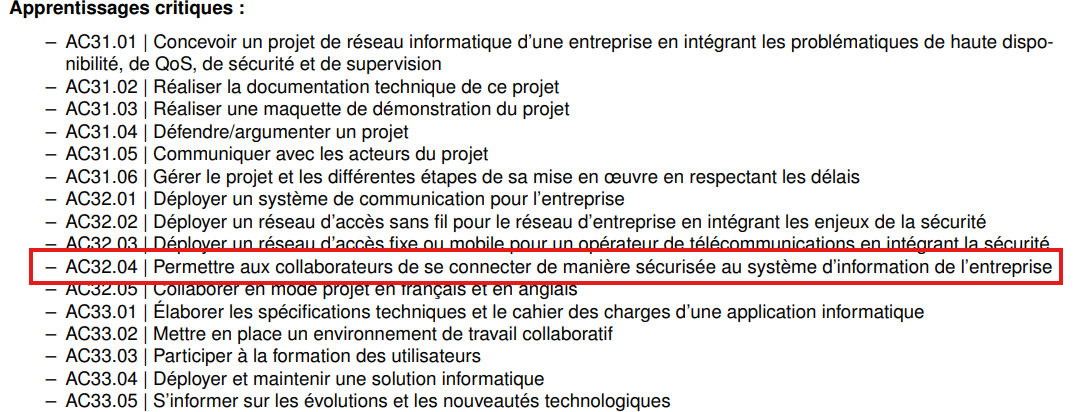
An entire private server structure for the game World of Warcraft (running on AzerothCore)
⚠️ DISCLAIMER : RTRealm is a private educational project created for learning purposes only. This project is not affiliated with, endorsed by, or connected to Blizzard Entertainment in any way. World of Warcraft, WoW, and all related content are trademarks and properties of Blizzard Entertainment Inc. This server is maintained solely for educational and non-commercial use within an academic environment.
My server is running on AzerothCore which is an open-source MMORPG framework. It is written in C++ and is based on the TrinityCore project. AzerothCore allows developers to create and manage private servers for World of Warcraft, providing a platform for customization and expansion of the game.
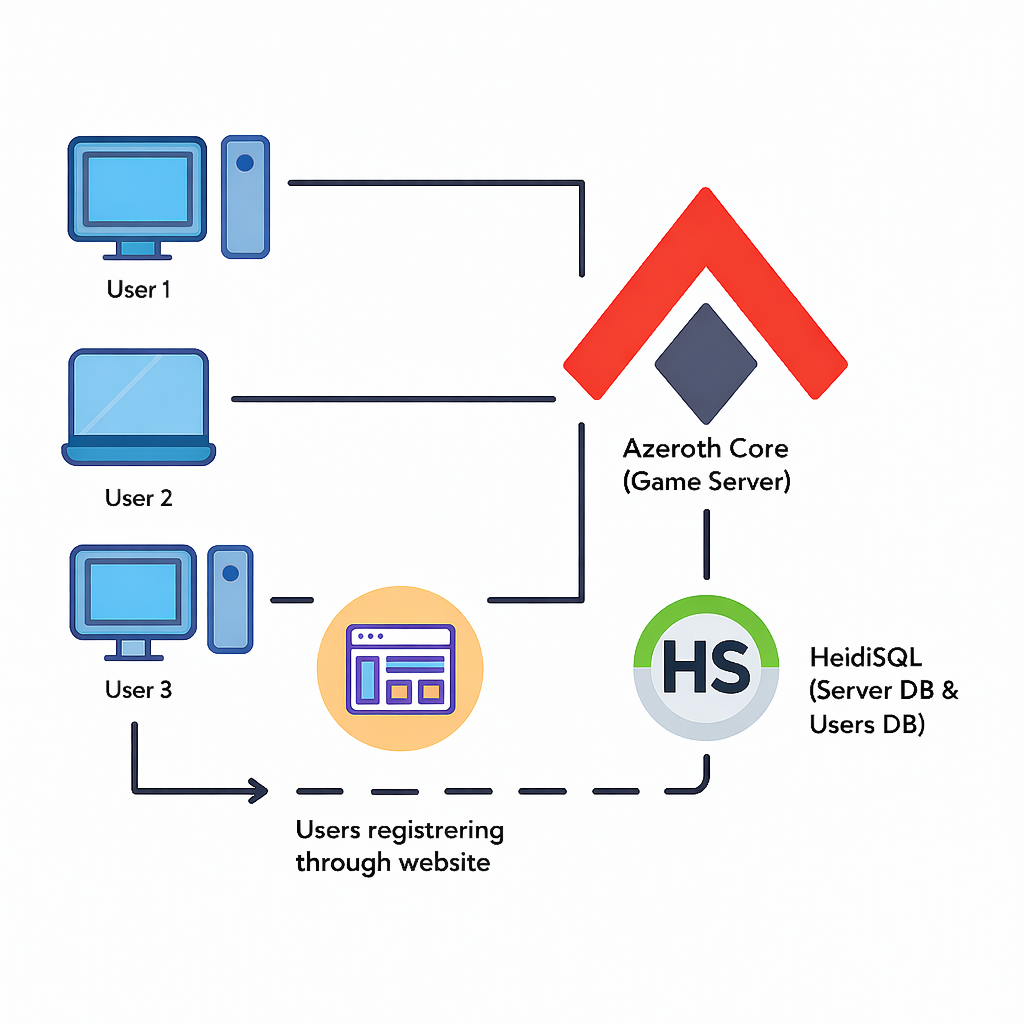
For the database i chose to use HeidiSQL which is a powerful and easy-to-use interface for managing MySQL, MariaDB, and other database systems. It provides tools for database design, query execution, and data management.
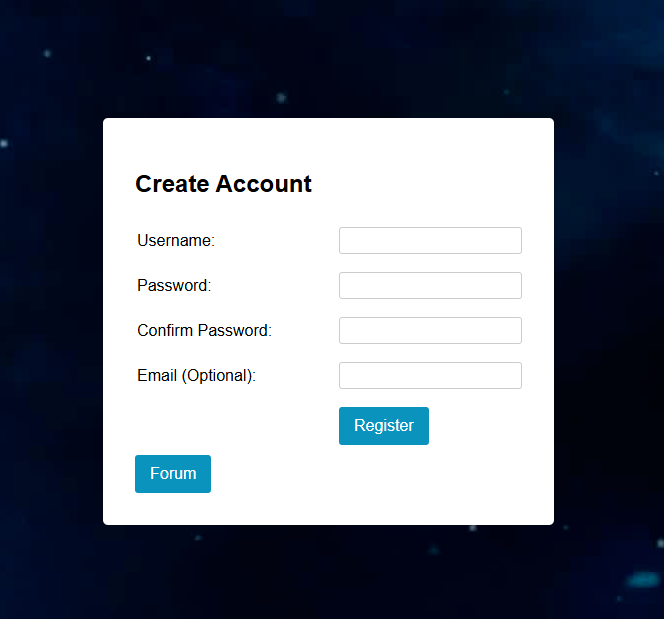
Users can create an account on the following website : RTRealm
The database has it’s own user, that is used only for this sole purpose, and has limited permissions to avoid any potential security risks.
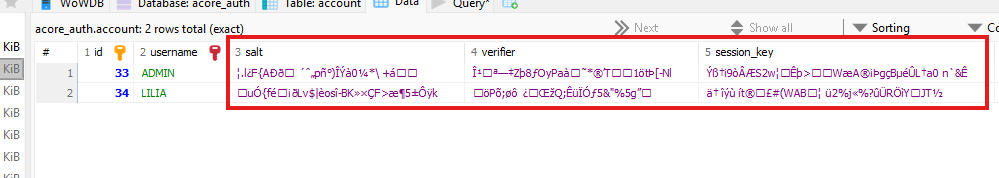
The server’s database is secured by hashing user details such as passwords, session key and salt using the SRP6 algorithm. This ensures that even if the database is compromised, the actual passwords remain protected. (More details in paragraphs below)
Here, users will be able to create their account. They will have to chose a password that is long and complex enough to ensure a good level of security (8 characters are needed).
The newly created account will be stored in the database with the following details : the account name, a salt (a random string of characters that is used to enhance password security), the verifier (a value derived from the password and salt using the SRP6 algorithm), and other relevant information such as email, joindate, last_ip, etc.
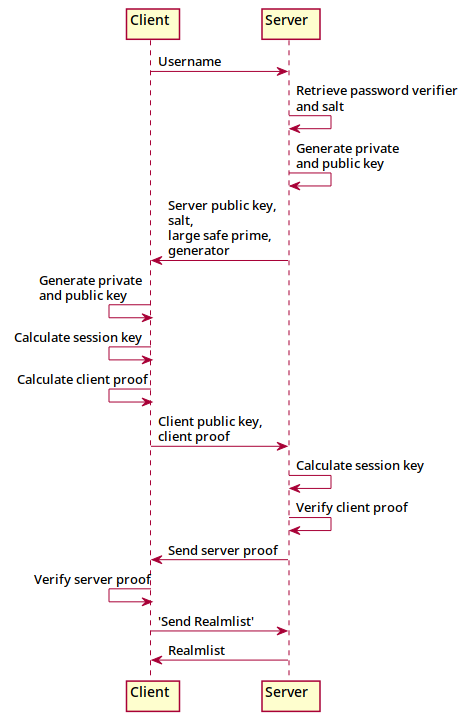
SRP‑6 is a version of the Secure Remote Password protocol designed to let a client and server authenticate each other without ever sending the actual password across the network. It works by having both sides generate their own private and public values, exchange only the safe public parts, and independently compute the same shared session key using a mix of large‑prime math and the stored password verifier.
Because the password itself is never transmitted or exposed, SRP‑6 protects against eavesdropping, replay attacks, and server‑database leaks where an attacker only obtains the verifier. The protocol ends with both sides proving they derived the same key, giving you mutual authentication and a secure foundation for the rest of the session.
Here you can see an example of the salted and hashed password stored in the database, along with the other account details.
Here is a video demonstration of the server in action, showcasing the register and login process. The database interactions are also highlighted to illustrate how user data is securely managed when a registration occurs.
This project directly demonstrates knowledge in several critical learning outcomes such as:
AC34.01 Cyber - Implementing Advanced Network Infrastructure Security Tools
CE3.05 - By integrating security issues
CE4.01 - By aiming for a fair compromise between security requirements and usability constraints
CE4.02 - By “respecting” standards and the legal framework
Through the deployment of RTRealm, I configured secure authentication mechanisms and implemented layered security protocols to protect the game server infrastructure from unauthorized access.
AC34.04 Cyber - Proposing Secure Information System Architecture for Small Structures
I designed and implemented a complete secure architecture for the RTRealm server, including proper separation of concerns between the game server, database layer, and user-facing registration system, ensuring data integrity and confidentiality.
AC36.01 Cyber - Monitoring System Activity
Account management and transaction logging were integrated to monitor user registrations, login attempts, and authentication failures, providing audit trails for security monitoring and incident response.
AC32.04 - Enabling Secure Employee/User Connection to Enterprise Information Systems
CE1.02 - By respecting fundamental principles of computer security
The SRP6 authentication protocol ensures that users can securely connect to the server without exposing their passwords over the network, implementing best practices for secure remote authentication in networked environments.
These implementations showcase practical application of network security, system administration, and database security principles essential to the N&T curriculum.